Revision [34478]
This is an old revision of HomePagePlus made by coolpup on 2026-02-16 03:26:34.
Reject proprietary computer operating systems that track, surveil, profile and manipulate the user.
Employ alternative systems that are superior, comprised of free software and respect one's privacy.
Puppy GNU+Linux is better than Microsoft Windows 10 & 11.
It is time to switch to Linux!
Tip: Use Grayjay
Desktop Computer Operating System Releases
A. Puppy GNU+Linux
- Using Debian package repositories
- see HomePage
- Using Slackware package repositories
- Using Ubuntu package repositories
- F96-CE
- Using Void package repositories
B. EasyOS GNU+Linux {experimental, cutting-edge 64-bit GNU+Linux computer operating system from Barry Kauler}
C. Fatdog64 GNU+Linux
D. Other Computer Operating Systems (for comparision with those above)
- 64-bit disk image only
- 64-bit disk image only
- 64-bit disk image only
- 64-bit disk image only
- 64-bit disk image only
- 64-bit disk image only
Flashing/Writing Desktop Computer Operating Systems to Data Storage Device
- Flashing to External Data Storage Device
- Flashing to Internal Data Storage Device
Flashing/Writing Android-Based Operating System Releases (Custom System Images) to Mobile Computer (Smartphone/Tablet)
https://eylenburg.github.io/android_comparison.htm
- Flashing
- Samsung Galaxy Tab S7 (LTE) - SM-T875 - gts7l
- Enable Developer options of target Android device/computer (gts7l)
- Enable OEM unlocking, from within Developer options
- Enable USB debugging, from within Developer options
- Reboot the target Android device/computer to Download Mode
- Unlock the bootloader
- Download these three image files & flash them to the target Android device (gts7l):
- iode-[...]-recovery.img
- iode-[...]-vbmeta.img
- Flash the third file using Recovery (from within the target Android device)
- iode-[...]-ota.img
- News & Reviews
- Distrowatch.com, 2025-11-05.
- Distrowatch.com, 2025-02.
- Community Forum

- Flashing
- /e/OS Web installer (open within chromium-based browser, e.g. Brave; for officially supported devices only)
- DevWithZachary, 2025-01.
- News & Reviews
- DistroWatch Weekly, 2022-07

- Flashing
Flashing/Writing Android-Based Operating Systems (Generic System Images) To Mobile Computer (Smartphone/Tablet)
- Method
- Samsung devices
- Non-Samsung devices
- Software Drivers
- Google U.S.B. Driver for Windows
- Samsung Android U.S.B. Driver for Windows
- Other O.E.M. U.S.B. Drivers
- Software Tools
- iodéOS G.S.I.
- /e/OS G.S.I.
- lineageOS G.S.I.
- developer misterztr
- developer doze-off
- lunarisOS G.S.I.
- Project Infinity X G.S.I.
- Android Open Source Project G.S.I.
Non-Android-Based Operating Systems for Mobile Computer (Smartphone/Tablet)
Privacy & Security
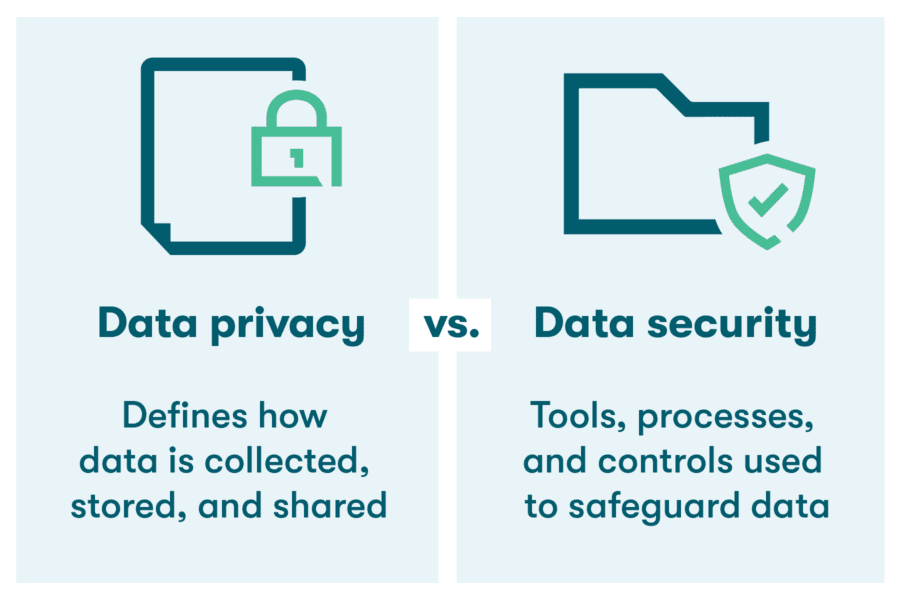

privacy: freedom from unauthorized intrusion (Merriam-Webster)
security: measures taken to guard against espionage or sabotage, crime, attack, or escape (Merriam-Webster)
cybersecurity: measures taken to protect a computer or computer system (as on the Internet) against unauthorized access or attack (Merriam-Webster)
- Internet Search Engines
- The Linux Experiment, 2025-05-22
- Browser Isolation
Confine any GoogleId. and minimize browser fingerprinting via strict Web browsing segregation (BrowserIsolation), by employing a different Web browser, for each of the following three circumstances:
- For when accessing Google services only & signed-in to a Google account (i.e. GoogleId. is present), e.g. Gmail, Youtube:
- Chrome FOR DESKTOP OPERATING SYSTEMS ONLY
- Brave FOR MOBILE OPERATING SYSTEMS ONLY
- For when accessing Google services only & not signed-in to Google account, e.g. Youtube
- For when accessing everything else & not signed-in to Google account MAKE THIS THE DEFAULT BROWSER
- LibreWolf, Floorp and Tor Browser can be used to segregate into further categories:
- Banking/Finance/Shopping
- Entertainment/General
- News/Politics/Health
- Linux Desktop Security: 5 Key Measures, Explaining Computers, 2025-10-05.
Backup
DataRecovery
SecureErase
Hardware

- Recommended Linux-compatible Notebook Computers, Rob Braxman Tech, 2025-10-01.
- Why we are at a fork with computing devices, Rob Braxman Tech, 2025-05-29.
- Laptop Confusion in 2025, Rob Braxman Tech, 2025-05-28.
- Choosing PC Build Components, Explaining Computers, 2025-03.
- Very Useful Small Computing Things, Explaining Computers, 2024.
- Oneplus Pad 3
Data Storage
- Solid State Drives
- Hynix P41 PCIe 4.0 NVMe M.2

- Flash Memory Cards



- The best microSD cards in 2025, Engadget, 2025-05-29.
- Testing MicroSD Express, Explaining Computers, 2025-06-29.
- Top S.B.C. microSD Card, Explaining Computers, 2020.
Software Applications (Apps)
Please consider contributing financially to support software developers.- Thunderbird: APK (Android package)
- SimpleX: {APK (Android package) | terminal app for GNU+Linux}
- JW Library: {APK (Android package) | ZIP for Windows}
- Run Any Windows Application On Your Linux Machine, Mental Outlaw: https://www.youtube.com/watch?v=mdnbIXArwVk
Networking
- I.P. Address
- Internet Speed
- Network Cabling
- Bombal, 2025.05
- Home Network Setup
- Basic
- Advanced
Programming
- Will Artificial Intelligence Replace Programmers?, Mental Outlaw, 2025.05.21: https://www.youtube.com/watch?v=QbiXTedaoSY
Playtime
Disclaimer
All information is provided in good faith, for educational purposes only, by content creators who cannot be held liable for any negative consequences. Use this information at your own risk. Do your own research and make sure of all things.
Home | HomePage | AdminPages | PageIndex | RecentChanges | RecentlyCommented | Forum

